Passwords and password managers
In this article, we’ll explore the common pitfalls associated with passwords, the advantages of using a password manager, and strong password practices to minimize the chances of a bad actor gaining unauthorized access to our personal information.
Passwords are our first and, at times, only line of defence in securing our online accounts and identities. They are used with almost every online service because they provide companies with a quick and easy way to onboard users and offer a simple way for those users to access their accounts.
While they are meant to keep our data secure, the trouble is, most of us use our passwords in an insecure way. Ultimately, we leave our emails, social media accounts, and potentially, even our money, exposed to the possibility of unauthorized access.
The Trouble with Passwords
Over the past 20 years, the proliferation of web services means that many of us now have dozens of online accounts. Having to choose and remember a new password for each of these websites can quickly get overwhelming. As a result, many of us have adopted a relatively standard way of choosing and storing our passwords.
Typically, when asked to choose these codes, we pick a word or two we care about, then capitalize the first letter and/or add a number or symbol when prompted to do so. To make things easier to manage, some 59% of users have even been shown to reuse the same password or variations of the same password across multiple platforms.
While these practices seem like a good way to ensure our passwords are not forgotten, most of the time, the simple passwords we create are among the first to be guessed with common password cracking algorithms used by internet hackers. In fact, standard brute force attacks, which generate and test all possible combinations of characters of a certain length, are able to crack an 8-character password in less than one second.
By not safeguarding our logins and by re-using login information across multiple platforms, we leave ourselves vulnerable to these kinds of attacks.
To put it into context, if one of our accounts is compromised, a digital thief will have instant access to any other account where that password is duplicated.
Have Our Passwords Been Compromised?
The website haveibeenpwned.com, created by security expert Troy Hunt, allows us to enter an email address to see if our online account information and passwords have been leaked from a data breach. It also lets us subscribe to breach notifications for any email we’d like to track.
To ensure that our accounts remain secure, we recommend visiting this site on a regular basis to search all email addresses. If a hit is found, we suggest changing the passwords on those websites immediately along with any other websites that use the same passwords.
Now, let’s get practical!
Choosing a Strong Password
The basics:
- DON'T use a password made with a simple selection of words, names, addresses, birthdays, or any personal information. These will be too easy for a person or computer to guess.
- DON'T use common song lyrics, book passages, internet queries, or memes for passwords. These too, while seemingly unique, can be easy to guess.
- DON'T use predictable patterns typed on a keyboard (e.g. “qwerty”, “asdfghjkl”, or “!@#$%^&*”).
- DON'T use the same password across different sites.
- DON'T use a password that has shown up in a past breach.
- DO use a password generator to both generate and keep track of unique passwords for each site. Generally, a longer password is harder to crack.
- Using passphrases (a string of random words) can be very secure while staying easy to remember.
Some further tips on practicing good password hygiene: - Don’t write passwords on sticky notes and leave them lying around. Passwords written in a notebook and stored in a desk are not very secure either. If you write down hard copies of a master password and other encryption keys, keep them locked in a vault, safety deposit box, or some other secure location.
- Don’t store bitcoin private keys or seed words (or those of any other digital asset) in your password manager.
- Don’t store 2FA backup codes or seed words in your password manager. Store them in a secure location like a vault instead.
- Turn on 2FA for your password manager app using Google Authenticator and/or get a Yubikey.
- Take extra care to lock up any account that can be used to log into or reset other accounts’ passwords, such as your primary email, or Google, Twitter, Facebook, and Apple accounts.
- Learn how to spot and protect against phishing, whether it’s through SMS, email, or a variety of other methods.
If we take all of these steps, we should have better control over our passwords and accounts than 99% of the population.
This XKCD classic comic perfectly illustrates the process behind choosing effective passwords
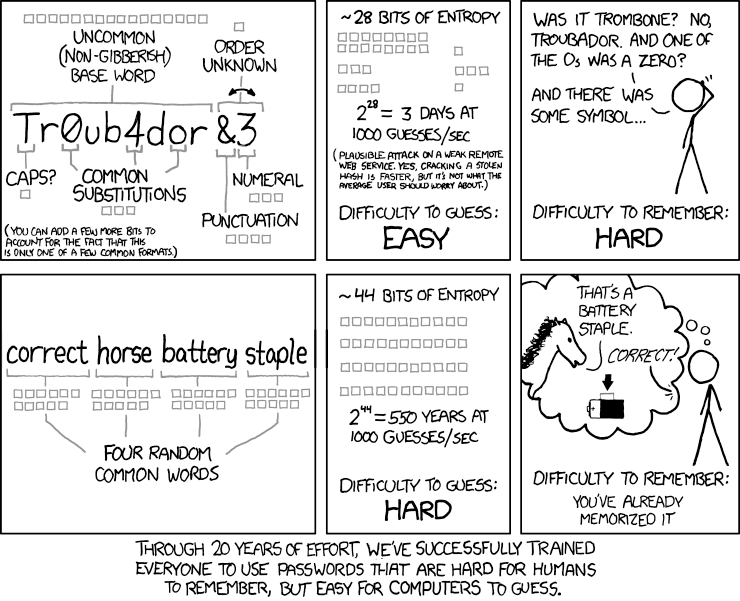
In a visual way, this comic introduces us to the idea of entropy being the most important consideration when choosing strong passwords. Entropy, when it comes to passwords, is a mathematical measure of how difficult it is to guess a password by knowing how it was derived. Simply stated, it’s a measure for a password’s randomness.
The math behind choosing strong passwords is a fascinating topic. For more on password entropy, you can check out our technical companion post: “Password entropy? What’s that?”
How Long Should Our Passwords Be?
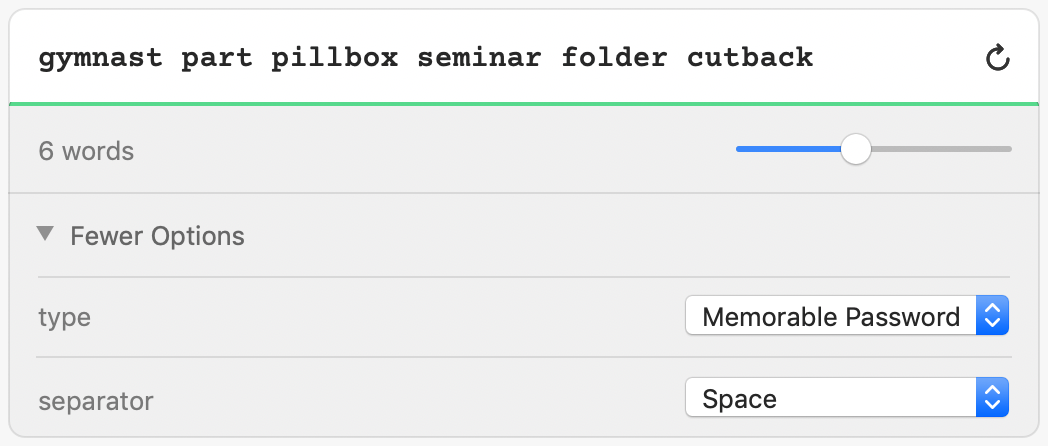
While many sites suggest at least 8 characters, with our most important sites, we recommend a minimum length of 15 characters for randomly generated passwords and 6 words for randomly generated passphrases. These will provide at least 80 bits of entropy and can be considered to be very strong passwords — more than strong enough to secure our precious online accounts.
Passwords or Passphrases?
To maximize the protection of our accounts, security experts and researchers are now beginning to recommend passphrases instead of traditional passwords to secure our accounts. While a lot of people have taken this to mean that “passphrases are better than passwords,” the truth is more nuanced than this.
Per-character, randomly generated passwords are actually stronger than randomly generated passphrases. However, the benefits to passphrases are that a short list of 4-6 words is easier to remember than a longer list of 12+ characters, and even if someone makes a passphrase off the top of their head, they will still typically be stronger than the most simple passwords that many of us use.
The challenge with using passphrases is that they don’t always fit into a site’s maximum password length permissions.
When we find ourselves restricted by the length of the passwords that we can choose, we recommend using randomly generated character-based passwords. These will give us the highest strength passwords for the space that we have to fill.
How to Generate and Manage Passwords
Password managers can generate secure passwords for us, remember all of our usernames and passwords, automatically plug them into websites, notify us of any breaches, store secure notes, sync changes across devices, automatically fill in forms, and much more.
These managers are especially needed since most of our newly generated passwords will look something like this:
dhu0Qbr1BfE1Ry5gnMYDNzZZqP5CzLagEoh^6%.p%#bAqHdPwXo5s
valved escapee bewail ungird behemoth ailment
Among the most popular options today are 1Password, Dashlane, LastPass, Myki, KeePass, and Bitwarden, though there are many others.
How to Choose a Password Manager
When choosing a password manager, there are certain factors to consider. It is important to know that it’s been around for a while, has a team that continues to actively develop it, and is fully supported on the platforms we might use (i.e. Mac, Windows, Linux, iOS, Android, ChromeOS, or other).
Most of the password managers we mentioned above share many of the same features; though, there are a few main differences between them.
Generally, all password managers encrypt our data and allow us to sync it to both the cloud and our various devices; but, we’ve found 1Password to be an enjoyable and easy solution to get up and running, with a full feature set, an excellent user interface, good documentation, and support across multiple platforms.
To keep data local, we recommend using an app like KeePass or MyKi.
KeePass is made for Windows but has a number of community ports for different devices. MyKi stores passwords in a database on our phones, where we authenticate login requests sent from our computers.
For open source options, Bitwarden and KeePass are both strong options. Open source allows developers to review the source code in these applications and this reduces the trust users have to place in their creators.
Some password managers will alert us of any poor or compromised passwords, either because they are too short, are being used with multiple accounts, or have shown up in a past breach.
The most important thing to do is to pick one password manager, test out its level of personal appeal, and then start using it to generate unique passwords for each of our online accounts.
Choosing a Strong Master Password
Password managers rely on one very strong password to secure its list of all our account logins. As one of the few passwords we’ll actually have to remember and one that we’ll enter almost every day, it’s important that we choose a master password that is at once strong, memorable, and easy to type. This password will protect the contents of our encrypted database as it syncs across the web to our various devices.
The ideal solution when choosing a master password is for us to use a randomly generated master passphrase. 1Password will pick words at random from a set of 18,000 words, where each additional word adds about 14 bits of entropy. A password of 6 words gives us approximately 84 bits of entropy and will make for an excellent master password.
We need to make sure that we keep the master password completely random without changing any of the words, or re-generating passphrases until we see words that we really like. Once we’ve generated our master password, it’s best to make sure we haven’t saved it among our password manager’s saved passwords.
Security Questions are Passwords too
Many websites give us the option of using security questions as a convenient way to reset our passwords, should we need to. Most of us set these when we create our accounts—writing our mother’s maiden name, childhood best friend, the street we grew up on, or the name of our first pet—only to forget having done so later. Later, when reviewing the security of our accounts, we might not consider security questions as a way for a hacker to gain entry, or how easy their answers would be to search for or guess.
That means it’s important to remember that answers to security questions are passwords too and should be treated as such. Rather than answering these questions in a straightforward and guessable way, it’s best to randomly generate passwords and store them in our password manager as an entry for each site. Like other passwords, we should take care to not reuse our answers to security questions across multiple websites.
Conclusion
We have completed an in-depth exploration of best practices for selecting and managing passwords, and keeping those passwords secure.
The most important things to remember are to:
- Use a password manager to randomly generate unique passwords (and security answers) for each of our accounts.
- Protect our devices from malware and physical intrusion
- Keep an eye out for emails and websites that might be phishing for logins
Taking all of these steps should give us greater peace of mind when it comes to our account security.
In the next article, we will delve deeper into our discussion about data security and explore the importance of 2-step verification when protecting our online accounts.
More Reading
- Toward Better Master Passwords by Jeffrey Goldberg of 1Password
- How to use a password manager by The Verge
- Microsoft Password Guidance by the Microsoft Identity Protection Team
- On Password Managers by Tim Bray
- Password Advice by Schneier on Security
- The Best Password Advice Right Now (Hint: It’s Not the NIST Guidelines) by Roger A. Grimes of CSO Online
- All 3 Billion Yahoo Accounts Were Affected by 2013 Attack by Nicole Perlroth of The New York Times
- The World’s Biggest Data Breaches and Hacks (visualization) by Information is Beautiful
- Strong Passwords NEED Entropy by Aaron Toponce
- Have I Been Pwned and Pwned Passwords by Troy Hunt
- Watchtower: We shall fight on the breaches by Rick Fillion of 1Password
- Why don’t we follow password security best practices? by Emily Cain
- Answers to password reset questions are passwords too — so why aren’t we treating them that way? by Mahmoud Al-Qudsi
- How I became a password cracker by Nate Anderson of Ars Technica
A special thanks to I.K. and Cydnie Smith for their contributions to this article.

